Broadcom’s Acquisition of VMware Closed: What Now?
The long-announced acquisition of VMware by Broadcom back in May of 2022 closed November 22, 2023, having finally received the blessing of the Chinese regulators, the last hurdle. Now that they have made it official, it’s time to revisit our article on this almost a year ago this month (VMware’s Fiscal Year End and Broadcom’s Acquisition Implications). In that blog, we encouraged VMware customers to plan ahead and understand Broadcom’s culture and motivations for the acquisition – and plan accordingly. Business (not) As Usual We are currently seeing many VMware deals put on hold pending more reviews during this newlywed phase. Getting ...
Read More
Crowdstrike: Fiscal Year End and Analysis
Product Summary: Crowdstrike is best known for their cloud-based endpoint protection and response (EDR) solution to detect intrusions across networks and endpoints. The flagship product is Falcon that includes a suite of security products that strive to protect the enterprise against malware and threats in real-time with deep threat intelligence. Arguably, they are known for the breadth and depth of their threat intelligence to identify malicious code or other threats before they do damage or spread across the network. The company claims that its technology can detect 99% of all malware threats before they impact your organization or ...
Read More
VMware Fiscal Year End and Broadcom's Acquisition Implications
Big changes are in store for current and soon to be VMware customers. And wherever we see big changes with our major suppliers, the fallout typically lands in two categories for their respective customers. 1) Those who see it coming and plan accordingly, and 2) those that take no action and let things happen to them. That latter category will end up paying a premium for years to come over their peers for the exact same products and services. With all the current happenings at VMware, now is the perfect time to analyze your current and or projected spend and plan accordingly so you can take advantage of this change, rather than become a ...
Read More
Be Skeptical of Suppliers Increasing Prices with Inflation Excuses
It’s a now well-known axiom that there is opportunity in chaos. From our vantage point, technology suppliers are joining in the spirit of that theme to accelerate price increases which are then passed along to their customers. Price gouging it would seem is no longer the domain of consumer goods as we suspect it’s also being employed in high tech. If you have been involved recently in a renewal, software audit, M&A activity, or any other supplier intensive negotiation, some of these price increase ‘excuses’ may sound familiar: Inflation Energy costs Interest rates Labor supply Economic downturn War in Ukraine Rising US dollar value ...
Read More
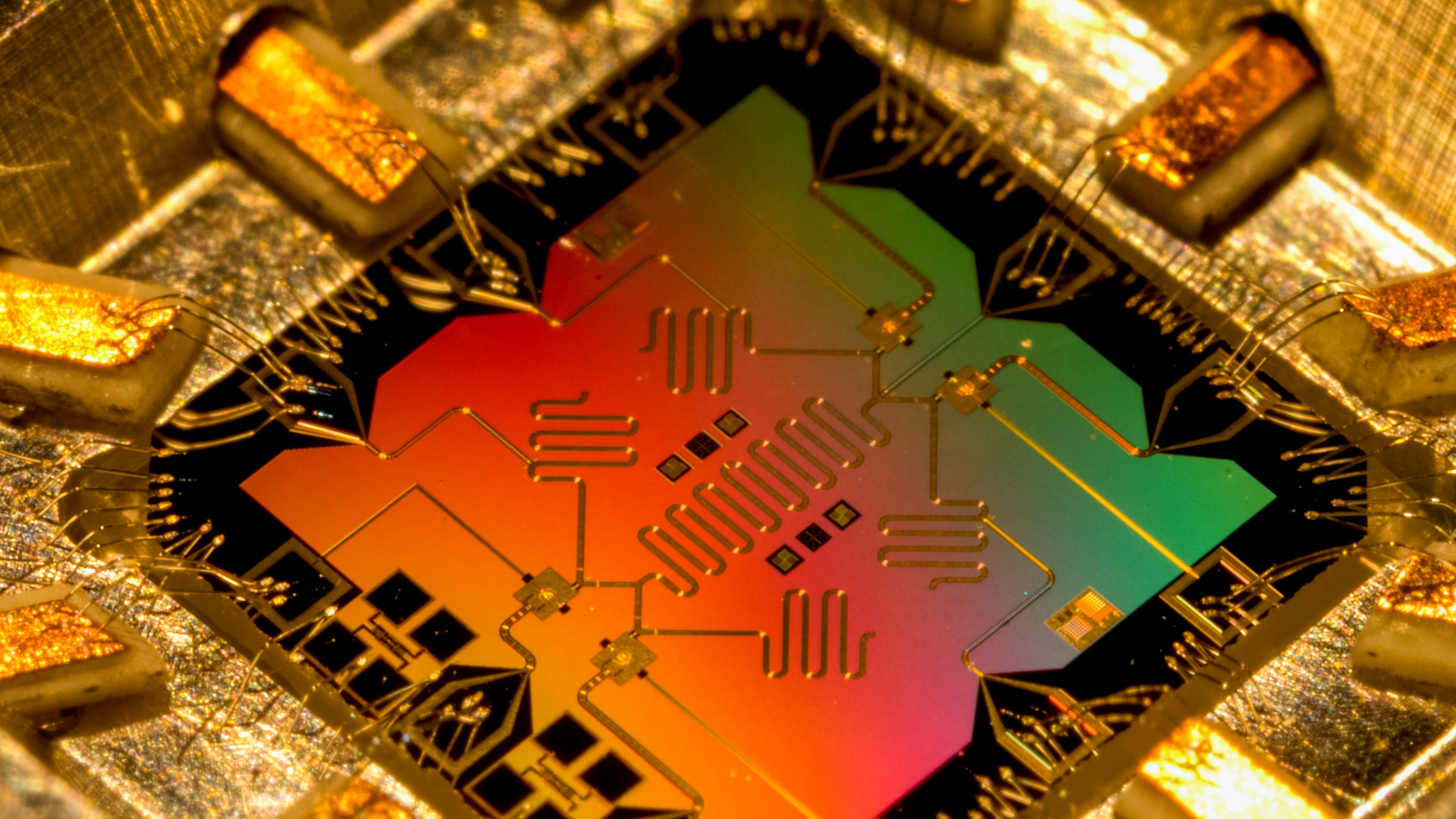
Enterprise Security: Getting Ready for Q-Day and PQC
Q-Day: The day quantum computers can render all current encryption methods meaningless. If you are not yet familiar with the terms Q-Day and PQC, you should be starting today. PQC or ‘Post Quantum Computing’ refers to the next wave of potential security headaches coming your way in the next decade if not sooner. The industry already has coined a term for it, called Q-day, which is when your current security that revolves around cryptography will be rendered irrelevant. So, this may be one area where being an early adopter has far less risk than being a laggard. The good news is that we seem to have some time to prepare for this change (more ...
Read More
Is Your Digital Strategy 5G Ready?
We get it. You've been deluged with the advertisements on television and social media from the major wireless carriers touting their 5G roll out, with hyperbolic comparisons touting that ‘their network’ is more available and robust than the competition. Mobile phone manufacturers are pushing the availability of their devices on 5G and how life changing it will be. Articles abound from all the business forums on IoT and 5G, and what a seismic shift it will be. 5G is also propelling this notion of Industry 4.0, and how it will accelerate that process. All this promise is, well, promising. But in the real world of managing a business, growing ...
Read More
Cyber Security and Ransomware: Punching Above Your Weight With MSPs and MSSPs
The news is rife lately with security breaches and ransomware attacks. The U.S. company Colonial Pipeline was among one of the high profile cases given the impact on business and consumers across the country. There have been several others such as JBS USA food processor, Ireland’s HSE (Health Service Executive) which manages health care system, Acer and many, many more. As an NBC news item recently put it, Cyber Security staff are barely hanging on and not able to keep up with the barrage of attacks. Its clear that for the short term, the opportunities for criminals to make vast sums of money are simply too good to resist and will likely ...
Read More
The Top 25 Cyber Security Suppliers for 2021
Call them what you will, but hackers, cybercriminals, and identity thieves, as well as some notable nation states, are an increasing threat to enterprises of all industries and sizes across the globe. The recent Colonial Pipeline ransomware incident is only the most recent and noteworthy because it impacted an important supply chain: gasoline. However, hundreds of similar breaches are playing out every day and it really goes without saying that Cybersecurity continues to be a top concern among businesses across industries, particularly as work environments have shifted from the office to the home. While Cybercriminals are attempting to ...
Read More
SolarWinds Breach: Three Lessons You Need to Heed
What do the Pentagon, the U.S. State Department, The White House, the NSA, all five branches of the US military, the top ten U.S. telecommunications companies, and four hundred twenty-five of the Fortune 500 all have in common? Given the title of this article, you already have a clue, which is that they are all SolarWinds customers. Those are just some of the higher profile organizations, but in all there are 300k SolarWinds customers around the world, with about 18k identified as impacted. The impact of this breach is so far and deep, the actual repercussions will not be fully understood for years potentially. However, we don’t have to wait ...
Read More
Cloud Cost Optimization: Moving Mountains With Shovels
The front lines of the Cloud Cost Optimization battle are not going well for many. Sadly, the worst part of the story is, that most don’t even know it yet. As Cloud investments go deeper and broader throughout corporate computing environments, so too is the waste and damage to IT budgets. I’ve been in IT long enough to witness hundreds of companies implement and manage thousands of different environments with hundreds of various suppliers. Suffice it to say, I’ve been around. So, when I tell you that waste and overspend on Cloud are at frightening levels, you should pay attention when I share why, and what you might be able to do about it. ...
Read More